In the age of advanced cyber security solutions, firewalls, and multi-factor authentication, it's easy to overlook a different type of risk to information security: the human element.
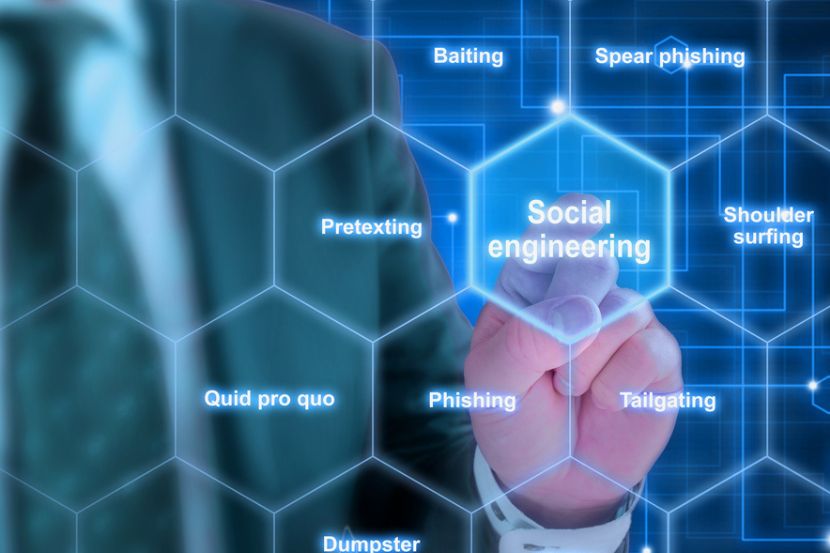
Social engineering attacks, which manipulate human psychology to get people into divulging information or performing actions that compromise security, are increasingly common and sophisticated. These attacks exploit human weaknesses rather than technological vulnerabilities, making them challenging to defend against using traditional security measures alone.
From phishing emails that seem to come from trusted colleagues to impostors masquerading as IT personnel, social engineering attacks take on various forms and present organizations with a multiplicity of challenges.
This article explains everything you need to know about social engineering attack prevention, including the most efficient techniques for protecting your data from these malicious attempts as a business and as an individual.

How Can Businesses Prevent Social Engineering Attacks?
Businesses must combine technological solutions with education on social engineering to protect themselves from these attacks.
Here are the methods you can implement to prevent a social engineering attack.
1. Performing Regular Security Awareness Checks
Providing security awareness training to their employees on a regular basis ensures that companies strengthen the first line of defense against social engineers. They must educate their personnel on potential social engineering attacks they could be exposed to, such as spear phishing, pretexting, tailgating, etc. By learning to recognize the telltale signs of these attacks, employees work together to block social engineering attempts and protect the organization.
A crucial part of security awareness training is performing vulnerability assessments to check the company’s preparedness for potential attacks. Simulations and mock social engineering attacks test not only the efficiency of your tech solutions but also the knowledge of the employees on this matter. Employees who fail these assessments should be required to take the training again to hone their ability to recognize social engineering attacks.
The importance of security awareness training is backed by the fact that over 85% of cyber security breach incidents are a result of a human element, according to Verizon. This shows that even the most advanced technology needs to be complemented by cyber-educated and quick-thinking staff.
2. Enhancing Access Protocols
Ensure that only authorized personnel have access to information and perform regular identity checks, especially if you suspect that an unauthorized attempt is taking place. Multi-factor authentication is an effective layer of protection from malicious attacks because it requires additional confirmation before granting access.
When it comes to money transfers, it is smart to require additional confirmation before initiating any financial transaction. For example, require a face-to-face confirmation before authorizing transfers over a certain amount. These protocols are essential protection from social engineering attacks since they directly address the errors humans make in daily interactions and put their companies in danger.
Social engineering criminals have created inventive methods of conducting these attacks without raising suspicion. Read about the most notable examples of social engineering attacks in recent history to learn how to protect yourself.
3. Conducting Email Filtering
Email filtering is an essential tool for preventing phishing and its subtypes, such as whaling, a social engineering method that targets company executives. Successful email filtering solutions are able to detect malicious content and flag it as suspicious before you open the email.
Email filtering also relies on sender verification, which detects suspicious domains and blocks their message or sends it directly to the spam folder. This prevents users from accidentally clicking on the message and engaging with harmful content. Some advanced email filtering solutions track “normal” behavior from trusted or frequent contacts. This helps them detect and flag unusual communication.
Verizon’s 2021 Data Breach Report states that 94% of malware was delivered by email. This, and the fact that an estimated 3.4 billion phishing emails are sent daily, highlights the importance of email filtering as a preventive solution.
Read our article on email security best practices that are easy to implement and effectively improve your security posture.
4. Employing an Incident Response Plan
Companies should have a detailed incident response plan in place for when a social engineering attack happens. This includes the steps to take to resolve the situation and prevent further damage to the company and its resources.
All incidents should be recorded for further assessment and reported to key personnel through proper communication channels. This provides the organization with a solution in case the incident happens again. It also shows weak points in the company system, as well as the human element that requires a keener eye.
5. Performing Regular Monitoring and Audits
Monitoring all network activity is one of the most efficient ways to detect and prevent a social engineering attack. Suspicious behavior should be reported to authorized personnel and analyzed to create an adequate solution before damage is done. These solutions should assess not only technical activity but also user behavior. For example, attempting to access the system at an unusual time by an employee who does not usually work during that time should be a red flag.
Regular audits help the organization identify weak spots in its systems and areas that could use improvement. They also check for compliance with the latest regulatory and industry standards, which goes a long way in data protection. Some companies hire third-party auditors who perform additional checks with a fresh pair of eyes.
6. Relying on Endpoint Security
Endpoint security ensures that all devices used by employees are protected with the latest antivirus, anti-malware, and other security solutions.
Endpoint devices such as computers, tablets, and work mobile phones are protected against social engineering attacks in several ways:
- Preventing access to unsecure websites and downloads of apps from unverified sources on company devices.
- Encrypting and regularly backing up all data so it remains inaccessible even if an attack happens.
- If the device is stolen or lost, the system should include a feature to remotely wipe all data to keep it protected.
According to research, over 98% of text messages get opened, which makes mobile phishing or smishing a highly successful tool for social engineering attacks.
7. Not Disregarding Physical Security
Only employees should have access to office spaces, server rooms, and company buildings. Staff must log all entries and exits, and security badges and biometrics should manage their access, particularly to areas containing sensitive data. Companies must set up surveillance systems within their premises to continuously monitor access.
Physical security is essential because it complements cyber security measures. For example, server rooms that house sensitive data need to be physically secure to prevent unauthorized access that could lead to data breaches. It's not enough to have firewalls and encrypted networks; if someone can walk right in and access a terminal, then digital security measures are rendered useless. The same applies to the daily work habits of employees. If an employee walks away from their workstation without locking it, this leaves room for data abuse, data theft, or malware installation.
Cyber security includes implementing strict physical security protocols to prevent unauthorized access to areas that contain sensitive systems. Read our article on the fundamentals on data center physical and digital security.
How Can Individuals Avoid Falling Victim to Social Engineering?
Social engineering attacks start with an individual falling for a trick and granting access or providing information they shouldn’t have.
Here is a list of the ways individuals can protect themselves from social engineering attacks.
- Remain on alert. Individuals should keep their eyes and ears open for suspicious behavior. If something seems off in your daily interaction, either online or in person, it is safer to report it to authorized personnel who will take care of the rest.
- Use strong passwords. Make sure your passwords are strong and changed regularly. Do not share them with anyone, not even if someone is claiming to be IT personnel.
- Limit online information sharing. This goes for not only company but also personal information. Beware of how you share your data online, including via email and social media.
- Verify all contacts. If someone is claiming to be a person of authority and asking for sensitive information, you should verify their identity through official channels rather than just the contact details they provided.
- Monitor personal account statements. By regularly checking your bank statements for suspicious activity, you can prevent unauthorized transactions and financial losses.
- Secure physical access. Make sure your workstation is always locked before leaving your desk, and never share your security badge with someone else.
Use phoenixNAP’s free password generator to create strong and complex passwords.
Building a Defense Against Social Engineering
As cyber threats grow in volume and sophistication, it is crucial to remember that the strongest firewall and the most complex encryption algorithms are only as effective as the people who use them. Individuals should do everything they can to avoid being the weak link in the security chain.
Companies should have a foolproof strategy that includes regular staff training, strictly enforced security protocols, and the latest technological solutions to mitigate the risks of attacks. phoenixNAP provides security features for your data and networks to keep your business covered and successful.



