Introduction
Disabling the firewall in CentOS is sometimes necessary for testing purposes. For security reasons, running a firewall on a production server is a must. We cannot stress enough the importance of a properly configured firewall management tool.
In this tutorial, learn how to enable and use firewalld on CentOS 7.
What is firewalld?
Firewalld is the default firewall manager on CentOS 7. It comes preinstalled and is active on the first boot-up. It uses both default and custom zones to allow or disallow incoming traffic.
Prerequisites
- A user with sudo privileges
- Access to a command line (Ctrl-Alt-T)
- A CentOS 7 machine
How To Check firewalld Status
Start by booting up your CentOS 7 server and checking whether firewalld is running. To do so, open the terminal (CTRL-ALT-T) and run the following command:
sudo systemctl status firewalldThere are several outputs you may receive.
Active: active (running)
If the output reads Active: active (running), the firewall is active. If you’re unsure whether the firewall manager started after a system reboot, consider issuing the following command:
sudo systemctl enable firewalldThat command configures the system to start the firewall after each server reboot.
Active: inactive (dead)
If the output reads Active: inactive (dead), the firewall is not running. Proceed to the How to Enable and Start firewalld section of the article.
Loaded: masked (/dev/null; bad)
The output might indicate that the service is inactive and masked. See the image below for further details.
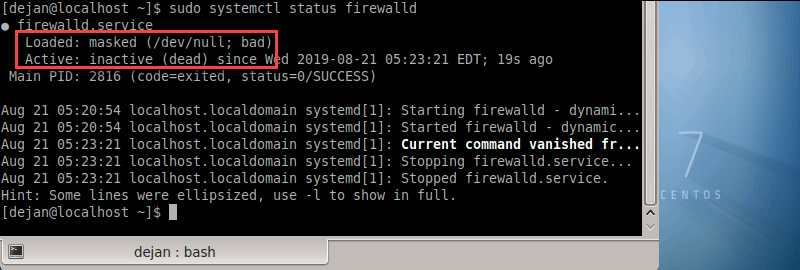
Here, the firewalld service is being masked with a symlink. Admins may mask the service so other software packages wouldn’t activate it automatically. You MUST unmask the service before enabling it.
To unmask the firewalld service, run the following command:
sudo systemctl unmask --now firewalldThe output should indicate that the symlink has been removed.
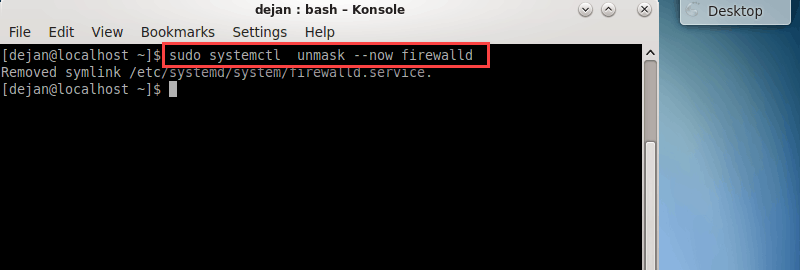
You may now proceed to the How to Enable and Start firewalld section of the article.
How to Enable and Start firewalld
To enable the firewall on CentOS 7, run the following command as sudo:
sudo systemctl enable firewalldAfter enabling the firewall, start the firewalld service:
sudo systemctl start firewalldWhen the system executes the command, there is no output. Therefore, it is wise to verify whether the firewall has been activated successfully.
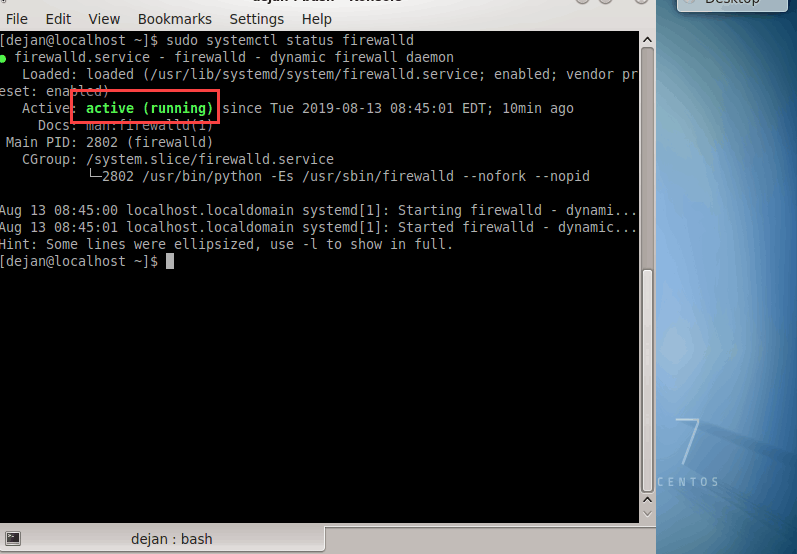
Check firewall status with:
sudo systemctl status firewalldThe output should indicate that firewalld is active and running.
Firewall Zones
Firewalld establishes ‘zones’ and categorizes all incoming traffic into said zones. Each network zone has its own set of rules based on which it accepts or declines incoming traffic.
In other words, zones govern over which packet is allowed and which is declined to function. This approach provides more flexibility compared to iptables as you can set different zones for the specific networks your device is connected to.
To view a full list of all available zones, type:
sudo firewall-cmd --get-zonesFor a fresh install, most likely you’ll get the following output:
Output
block dmz drop external home internal public trusted workThose are the pre-configured zones. To verify which zone is set as the default one, run the following command:
sudo firewall-cmd --get-default-zone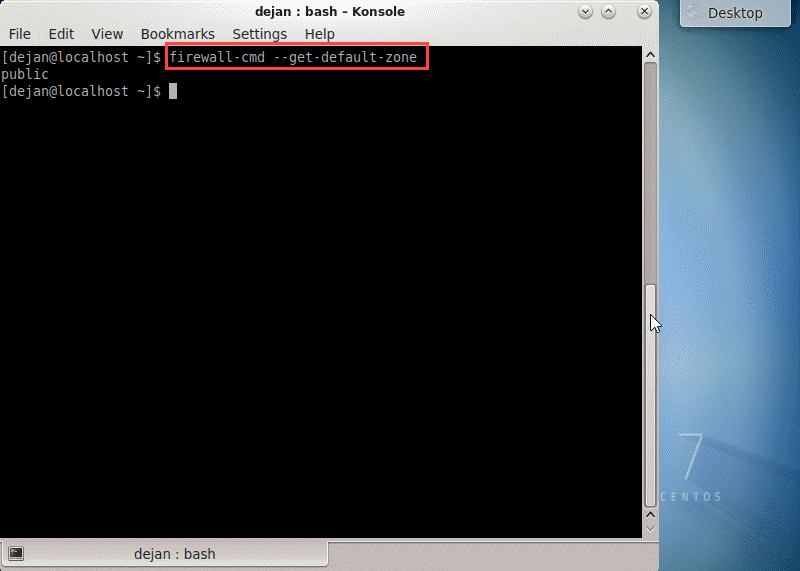
Firewalld has provided a list of all pre-configured zones and zone descriptions. The list below is ordered according to the level of trust, from the least trusted to the most trusted.
drop: The lowest level of trust. All incoming connections are dropped without reply, and only outgoing connections are possible.
block: Similar to the one above, but instead of simply dropping connections, incoming requests are rejected with an icmp-host-prohibited or icmp6-adm-prohibited message.
public: Represents public, untrusted networks. You don’t trust other computers but may allow selected incoming connections on a case-by-case basis.
external: External networks in the event that you are using the firewall as your gateway. It is configured for NAT masquerading so that your internal network remains private but reachable.
internal: The other side of the external zone, used for the internal portion of a gateway. The computers are fairly trustworthy, and some additional services are available.
dmz: Used for computers located in a DMZ (isolated computers that will not have access to the rest of your network). Only certain incoming connections are allowed.
work: Used for work machines. Trusts most of the computers in the network. A few more services might be allowed.
home: A home environment. It generally implies that you trust most of the other computers and that a few more services will be accepted.
trusted: Trust all of the machines in the network. The most open of the available options and should be used sparingly.
Verify Active Firewall Zone
To verify which zone is active, type:
sudo firewall-cmd --get-active-zonesThe output indicates the active zone as well as the network interfaces governed by it. If you don’t configure it otherwise, the default zone is the only active zone.
Firewall Zone Rules
To see which rules are associated with the default zone, run the following command:
sudo firewall-cmd --list-all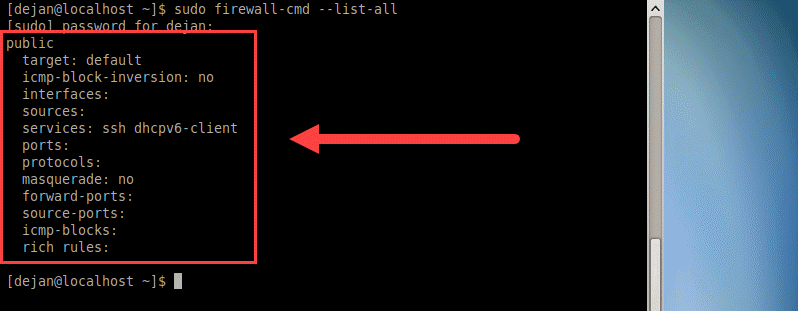
Let’s consider all the listed elements and define them:
target: Default indicates that the zone is a default zone. It may also indicate that a zone is active. In the example above, the public zone is not active, as it does not have any network interface associated with it.
icmp-block-inversion: This is an optional element which inverts icmp-block handling.
interfaces: All network interfaces governed by this zone.
sources: Sources for this zone (IP addresses).
services: Displays allowed services. In the example above, it’s ssh dhcpv6-client. For a full list of services available through firewalld, run the firewall-cmd --get-services command.
ports: A list of ports allowed through the firewall. It is very useful for allowing services that are not defined in firewalld.
masquerade: If none, then IP masquerading is disabled. When enabled, it allows IP forwarding. This effectively means that your server would act as a router.
forward-ports: Shows a list of all forwarded ports.
source-ports: Lists all source ports and protocols relating to this zone.
icmp-blocks: Displays blocked icmp traffic.
rich rules: A list of all advanced rules associated to the zone.
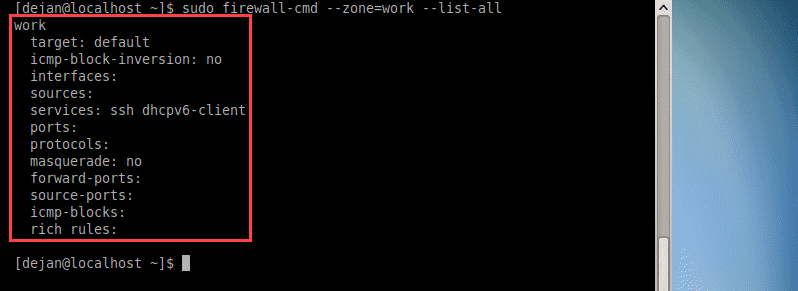
To get a list of rules associated to a specific zone, add the --zone= parameter to the --list-all command. For example,
sudo firewall-cmd --zone=work --list-allThe command above will generate a list of rules associated to the work zone.
How to Change the Zone of an Interface
It is easy to reassign another zone to a network interface. Use the --zone flag to specify the zone and then add the --change-interface flag to specify the network interface.
sudo firewall-cmd --zone=home --change-interface=eth1Verify whether the changes took effect:
firewall-cmd --get-active-zonesFirewalld should have applied the home zone on all traffic coming through the eth1 network interface.
Warning: When changing the zone of an interface, you may affect the status of active services. For example, if you’re working through SSH and move a network interface to a zone that does not support the SSH service, your connection might drop. Furthermore, you will not be able to log in.
Change the Default firewalld Zone
You can easily change the default zone. Use the --set-default-zone flag to indicate which zone you want to set as the default one. In the example below, we will set the work zone as the default one.
sudo firewall-cmd --set-default-zone=work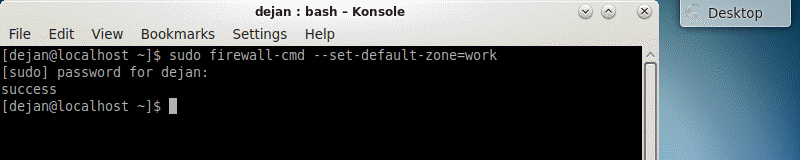
Upon changing the default zone, you should receive an output indicating that the change was successful. For further details, see the image above.
You may also verify the modification by running this command:
sudo firewall-cmd --get-default-zoneThe output should display that the work zone is indeed the default one.
Conclusion
By following this tutorial, you should have been able to successfully check firewalld status, as well as enable and start the firewall on CentOS 7.
We also covered basic firewall concepts, such as zones. You also learned how to manipulate the usage of default firewalld zones as well as how to unmask the service. All important first steps to understanding how firewalld works on CentOS 7.